
Apple has issued an emergency security warning to approximately 1.8 billion iPhone and iPad users worldwide, revealing that two zero-day vulnerabilities are being actively exploited in “extremely sophisticated attacks.” The company released iOS 26.2 to patch the critical flaws, which affect WebKit—the browser engine powering Safari and all iOS browsers—enabling attackers to compromise devices through malicious websites.
Zero-Day Vulnerabilities Explained
The vulnerabilities, designated CVE-2025-43529 and CVE-2025-14174, represent severe security flaws discovered by Apple Security Engineering and Google’s Threat Analysis Group. CVE-2025-43529 scores 9.8 out of 10 on the severity scale, while CVE-2025-14174 scores 8.8.
Both enable arbitrary code execution when users visit compromised websites, requiring no additional user interaction—a capability known as zero-click exploitation.
Targeted Attack Campaign Detected

Apple confirmed the vulnerabilities were exploited against “specific targeted individuals” rather than in widespread attacks. This targeting profile is consistent with mercenary spyware operations conducted by vendors like NSO Group, developer of Pegasus, and Intellexa, creator of Predator spyware.
These commercial surveillance tools are sold to governments and have been documented targeting journalists, activists, politicians, and human rights defenders across 150 countries.
Sophisticated Spyware Ecosystem

The mercenary spyware industry represents a multi-billion dollar ecosystem developing zero-day exploits for government surveillance. Pegasus can infiltrate devices through zero-click exploits, enabling complete device compromise including intercepting encrypted communications, accessing stored data, and activating microphones and cameras remotely.
Recent investigations revealed Intellexa has exploited at least 15 unique zero-day vulnerabilities targeting mobile browsers.
Affected Devices and Updates

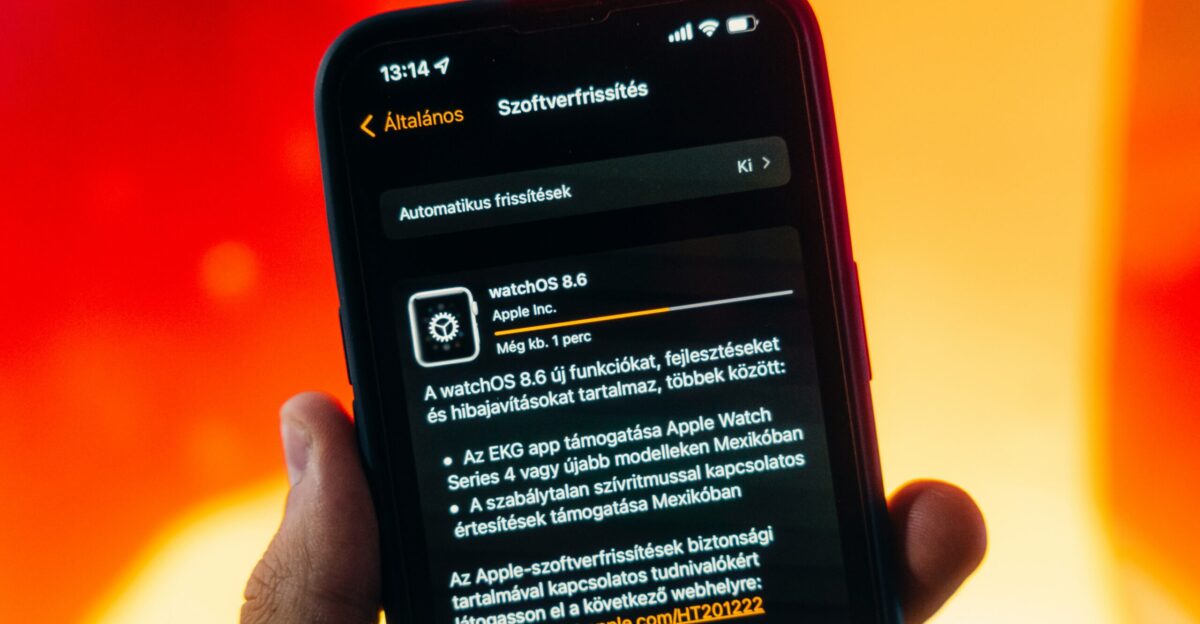
iOS 26.2 addresses the vulnerabilities across iPhone 11 and newer models, along with recent iPad generations including iPad Pro, iPad Air, and iPad mini devices. Apple released corresponding updates for macOS Tahoe 26.2, watchOS 26.2, and Safari 26.2.
Notably, users running older iOS versions can no longer update to iOS 18.7.3; Apple now directs all compatible devices to iOS 26.2 as the only security update path.
Comprehensive Security Patches

Beyond the two WebKit zero-days, iOS 26.2 addresses 26 distinct vulnerabilities, making it one of 2025’s most significant security releases.
The update includes a critical kernel vulnerability (CVE-2025-43462) that could allow applications to gain root privileges—the highest level of system control. Root access enables attackers to bypass app sandboxes, access all stored credentials and messages, and take over active banking sessions.
Background Security Improvements
Apple’s Background Security Improvements feature, introduced in iOS 26.1, automatically delivers lightweight security patches for Safari, WebKit, and system libraries between major updates.
Unlike traditional updates requiring user intervention, these patches install silently while devices charge and connect to Wi-Fi. The feature replaces Apple’s previous Rapid Security Response system, which faced adoption challenges and compatibility issues.
Apple’s Threat Notification System

Since 2021, Apple has sent threat notifications to users in over 150 countries when detecting mercenary spyware attacks.
In December 2025, Apple issued fresh warnings to users in at least 80 countries. These notifications appear at appleid.apple.com and arrive via email and iMessage, explicitly stating users are being targeted by mercenary spyware attempting to remotely compromise their devices.
Lockdown Mode Protection

Lockdown Mode, introduced in 2022, represents Apple’s most aggressive security posture for high-risk users.
When enabled, it blocks most message attachments, disables complex web technologies including JavaScript compilation, blocks incoming calls from unknown contacts, and prevents wired connections when locked. Apple states it has never observed successful mercenary spyware infections against devices with Lockdown Mode enabled.
Detection Tools Available

iVerify offers mobile threat hunting capabilities, scanning approximately 2,500 devices and identifying seven Pegasus infections since launching in May 2025.
The victims included journalists, activists, business leaders, and government officials. Amnesty International’s open-source Mobile Verification Toolkit (MVT) facilitates forensic analysis by checking device data against regularly updated indicators of compromise associated with known spyware vendors.
Rising Zero-Day Threat

The iOS 26.2 update represents the seventh and eighth zero-day vulnerabilities Apple has patched in 2025, reflecting intense targeting by sophisticated adversaries. The commercial market for zero-day exploits has grown substantially, with iOS exploit chains reportedly reaching millions of dollars.
This lucrative market incentivizes continuous vulnerability research, ensuring steady exploit supply for mercenary spyware vendors and state-sponsored actors.
Government Response and Sanctions

The U.S. Cybersecurity and Infrastructure Security Agency added CVE-2025-43529 to its Known Exploited Vulnerabilities Catalog, mandating federal agencies patch devices by January 5, 2026.
The U.S. Department of Commerce placed NSO Group on a trade blacklist in 2021, and expanded sanctions to include Intellexa in 2025. However, these companies continue operations by creating shell entities and restructuring across multiple jurisdictions.
Legal Accountability Advances

In May 2025, a California court ordered NSO Group to pay Meta $168 million for exploiting WhatsApp vulnerabilities to hack 1,400 accounts—the first time a spyware developer faced financial liability for capitalizing on smartphone system vulnerabilities.
Apple itself filed suit against NSO Group, accusing the company of targeting users in 150 countries. Despite legal pressure, the mercenary spyware industry continues thriving.
Immediate Action Required

All iPhone and iPad users should install iOS 26.2 immediately through Settings > General > Software Update. Users should enable automatic updates and verify Background Security Improvements is activated in Settings > Privacy & Security.
High-risk individuals including journalists, activists, and executives should consider enabling Lockdown Mode and conducting forensic scans through iVerify or professional security organizations.
Ongoing Security Vigilance

The persistent exploitation of zero-day vulnerabilities demonstrates that sophisticated surveillance threats have become continuous rather than exceptional. Technology alone cannot solve challenges posed by the global mercenary spyware industry.
Sustained vigilance, prompt security updates, international regulatory cooperation, and legal accountability for vendors and government clients remain essential for protecting users from surveillance abuse in an increasingly connected world.
Sources:
“About the security content of iOS 26.2 and iPadOS 26.2.” Apple Support, December 2025.
“Apple Issues New Spyware Attack Warning To iPhone Users.” Forbes, Kate O’Flaherty, 8 Dec 2025.
“iOS 26.2—Update Now Warning Issued To All iPhone Users.” Forbes, Kate O’Flaherty, 14 Dec 2025.
“Apple Warns of Zero-day Vulnerability Exploited in Attack (CVE-2025-43529).” U.S. Cybersecurity and Infrastructure Security Agency, 15 Dec 2025.
“About Apple threat notifications and protecting against mercenary spyware.” Apple Support, 2025.
“To Catch a Predator: Leak exposes the internal operations of spyware maker Intellexa.” Amnesty International Security Lab, 8 Dec 2025.
“iVerify Finds iPhone Zero-Click Compromise Threat.” Bastille Networks, 24 Sept 2025.
“CVE-2025-43529 | Threat Intel.” Lookout Mobile Security, 21 Dec 2025.